Hacking My Weekend Away: BITSCTF Edition 🔥💻
Alright, what better way to celebrate life than diving headfirst into a Capture The Flag (CTF) challenge, right? After what feels like a million years, I finally decided to spice up my weekend with some good ol’ hacking fun. And let me tell you, BITSCTF did NOT disappoint.
This CTF was a wild ride—some challenges had me questioning my life choices, while others were straight-up satisfying AF. But one thing’s for sure: this CTF seriously put my memory to the test 🧠💀.
There were quite a variety of categories including:
- CRYPTO
- HARDWARE
- WEB
- MISC
- FORENSICS
- WELCOME
- OSINT
- PWN
Anyway, enough of my yapping, enjoy the read:
Sanity Check
Category: Welcome
This was an easy one. All you had to do is join the BITSkrieg Discord server:
Flag
BITSCTF{W3lc0me_t0_BITSCTF}
Finders Keepers
Category: Forensics
I mean, how could I even be a blue teamer if I don't start a CTF with a forensics chall right? ( was mostly just steganography 😒 )
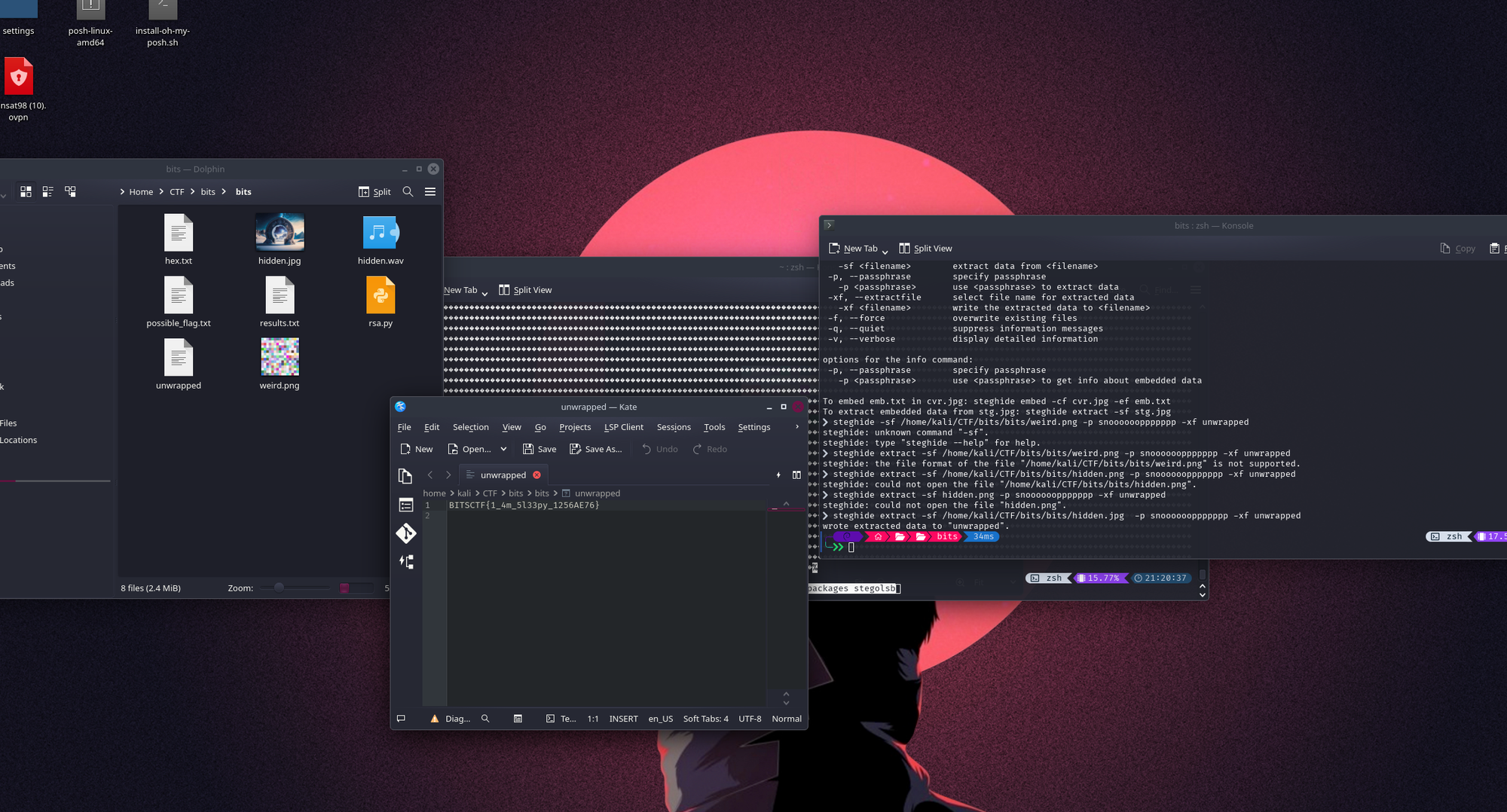
We are given the following image at first:
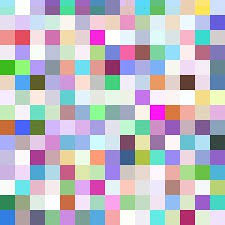
Like any other sane person, I tried to run this through Exiftool to check any weird metadata stuff, but found nothing other than usual boring png details.
But what if it was just a cover for something?
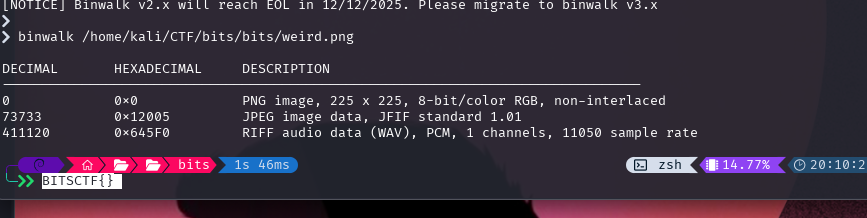
Used my go-to Binwalk to check if the weird file had other files within, and it did!
I managed to extract the following files:

Now the big question is: what the hell is that audio?
After a bit of thinking, I realised that the sound is just made of short and long beeps.. which can mean only one thing ( or one of many tbf): MORSE CODE!
Used my handy morse code decoder to translate the dots and the dashes of the audio to something that I can actually understand:
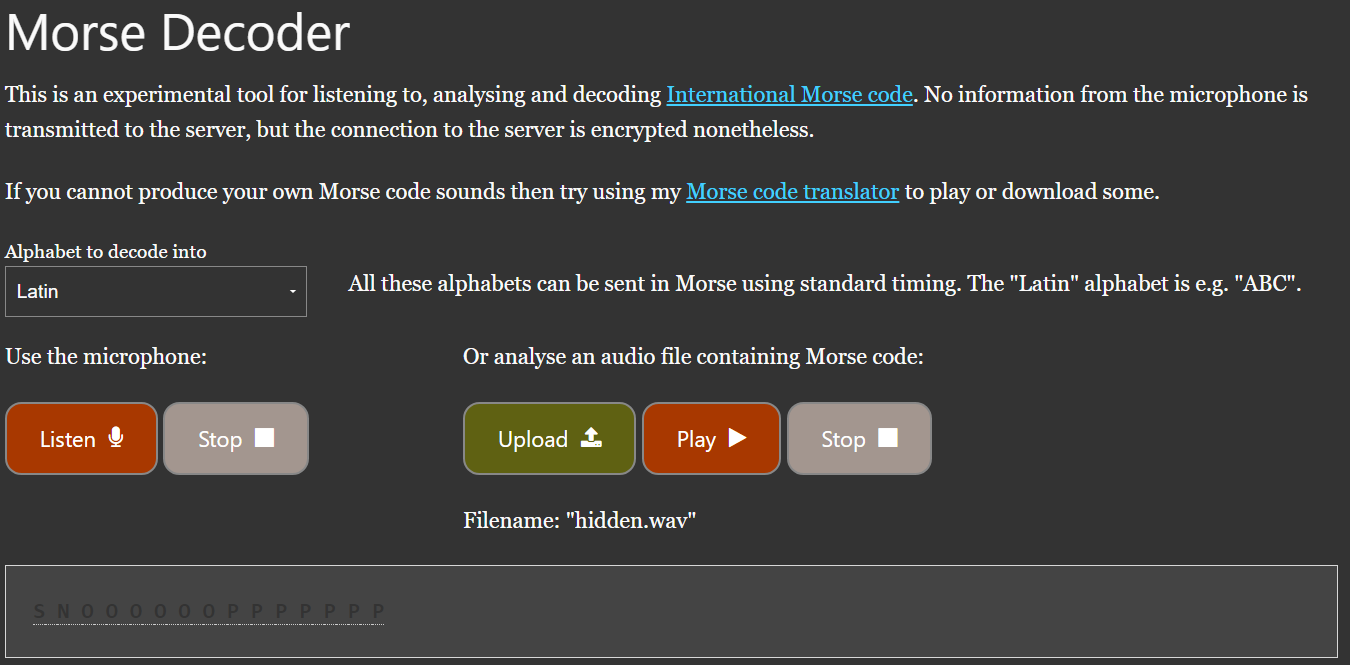
I mean... I thought I would understand it, but SNOOOOOOPPPPPPP isn't really a word. What could it be?
After some head scratching, I tried my luck to just use it as a password to see if the hidden.jpeg has more files hidden:
I used steghide to extract the files :
steghide extract -sf /home/kali/CTF/bits/bits/hidden.jpg -p snooooooppppppp -xf unwrapped
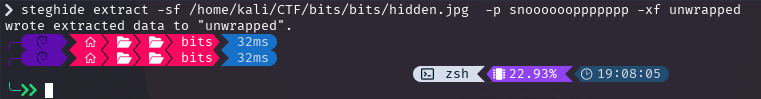
Et voilà: We found the flag!
FLAG
BITSCTF{1_4m_5l33py_1256AE76}

Baby DFIR
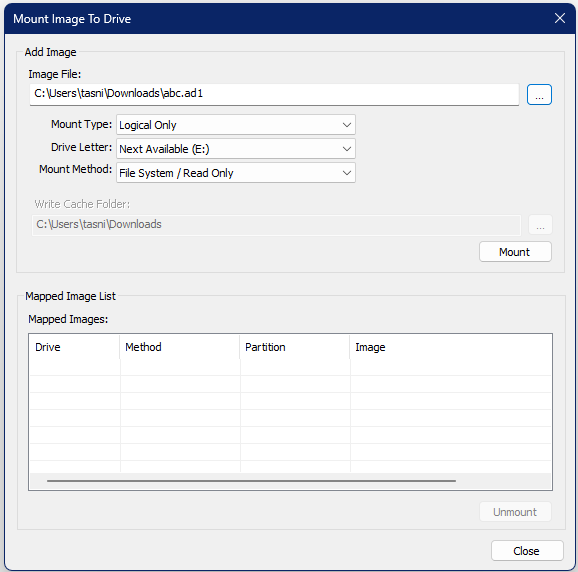
For this challenge, we are given an .ad1 file called abc.ad1
AD1 files are logical images similar to containers, where they hold file-level acquisitions.
At this point, the logical thing to do was to mount the logical image (puns intended) to my own host and try to view it's content using FTK Imager:
aaaaaaaaand got the flag:
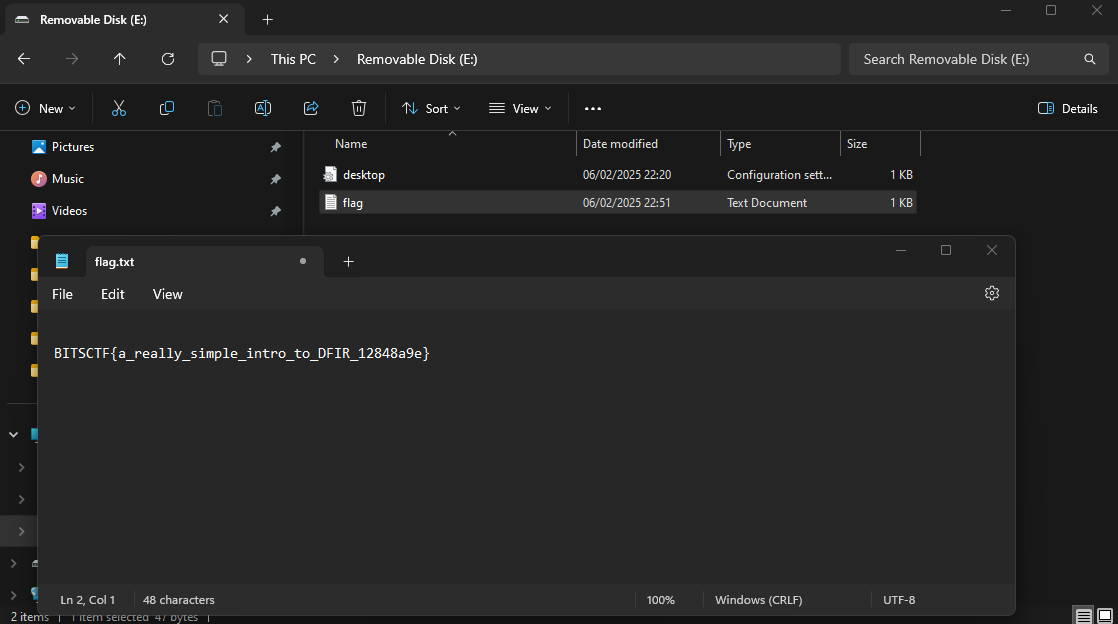
FLAG
BITSCTF{a_really_simple_intro_to_DFIR_12848a9e}